My Photo Stream is a boon for Apple ecosystem users, as it seamlessly syncs recent photos across devices and stores on iCloud. And though the images and videos are limited to your Apple ID, there can be security issues like an iCloud hack or device theft. Here are some My Photo Stream security tips and tricks to tighten your security settings to keep all these issues at bay.
How does My Photo Stream work with iCloud Photos?
Both My Photo Stream and iCloud photos automatically upload and sync across your Apple devices. A significant difference between the two is that My Photo Stream only keeps recent photos and not all photos.
Plus, My Photo Stream stores up to 1000 photos for 30 days and does not support live photos or videos. What’s great is that it does not count against your iCloud storage.
So, users who are short on cloud storage can use it to see and access their photos on Apple devices, Apple TV HD & Windows PC.
Like all technologies, My Photo Stream works as a boon and a bane. While helpful, it also increases the risk of your photos being discovered/found by some hacker getting into your account.
And as they say, precaution is always better than cure. Here are some security measures you must try.
How to protect My Photo Stream on iPhone
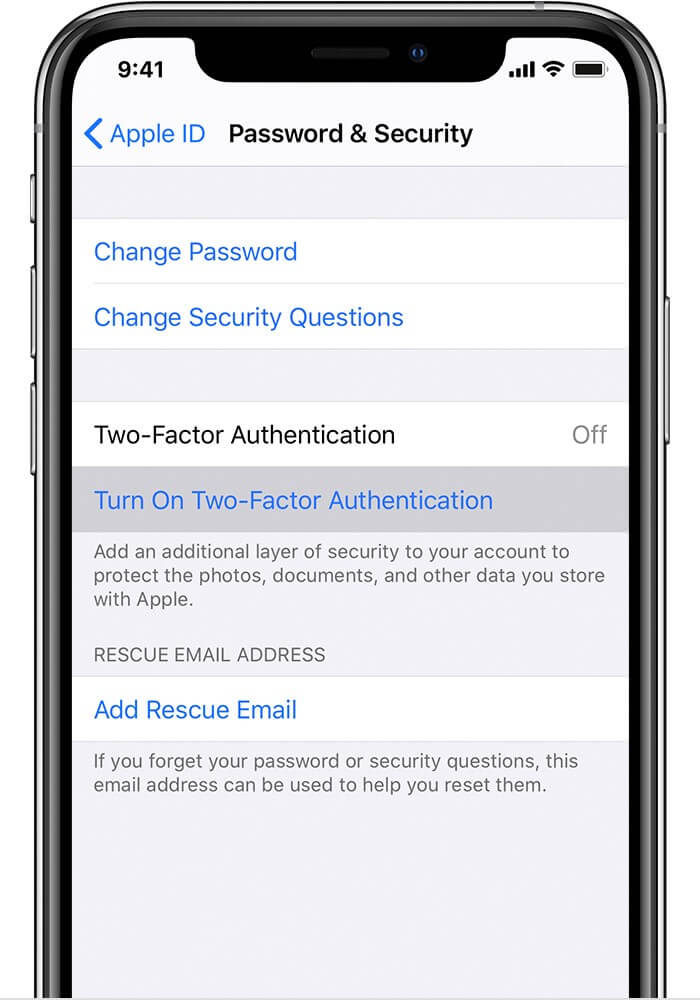
1. Turn on two-factor authentication for Apple ID
Add an extra layer of protection to secure your account with 2FA. When accessing your Apple ID from a different device, you will be prompted to enter a code along with your password.
So, even if someone can crack your password, they couldn’t access your account. Moreover, setting up the 2FA is pretty easy; check out our detailed guide for more info.
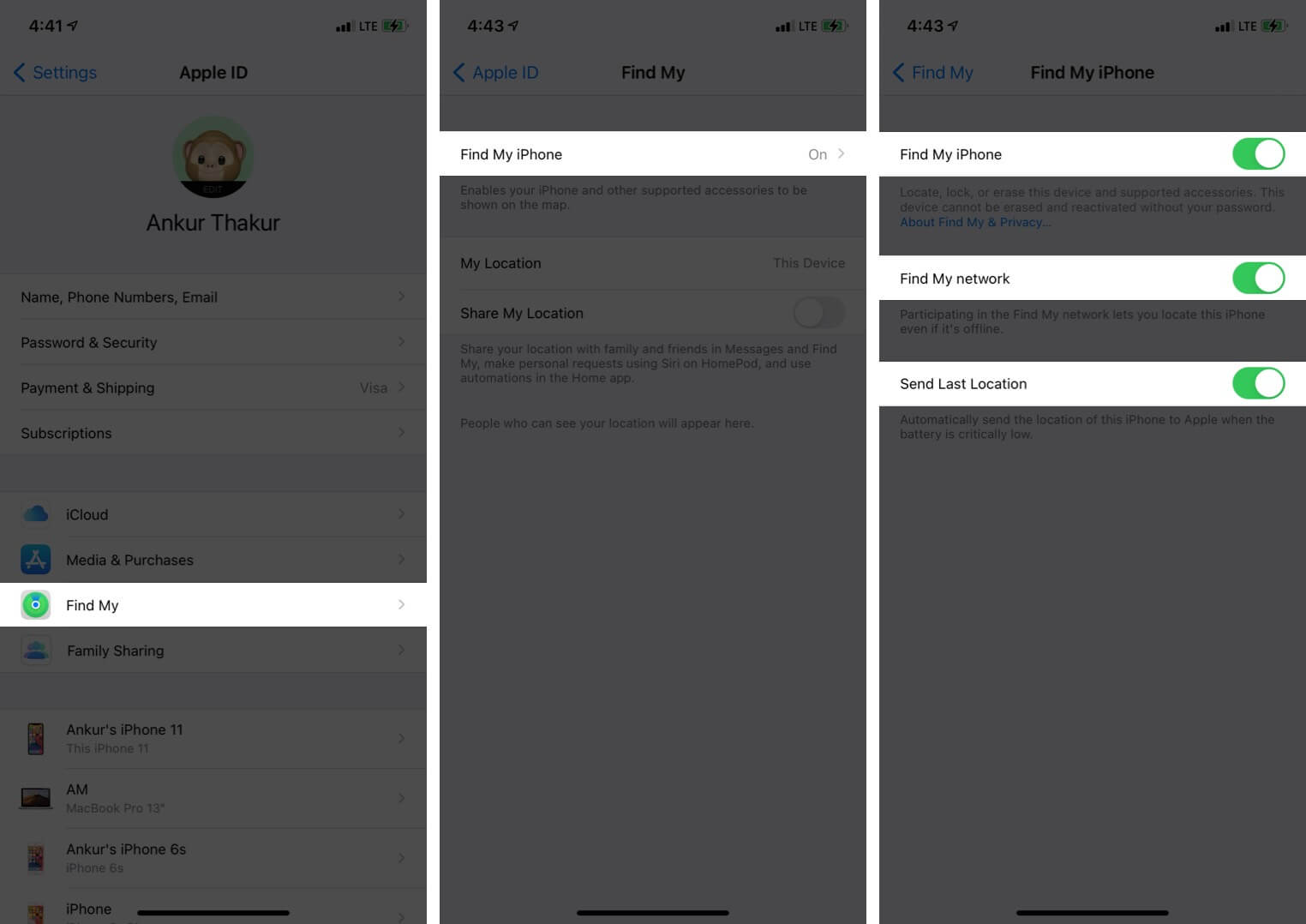
2. Ensure Find My is active on all Apple devices
No matter how careful we are, device theft could occur. Besides helping you find your device, Find My also comes in handy to remotely erase all your data, including My Photo Stream and Apple ID login.
To enable your Find My go to Settings app & tap on your name. Here, select Find My and tap on Find My iPhone. Now, Toggle On the switch next to Find My iPhone.
3. Regularly check and delete from My Photo Stream
Even though My Photo Stream stores it for 30 days only, it’s better to be vigilant. Check recently uploaded photos regularly and delete sensitive photos as soon as your work with them is over.
Another smart trick is to turn off the upload of burst photos on My Photo Stream unless you need them for some work. This might be a bit over-vigilance, but we are just overruling the risk of mistakenly sharing private images.
4. General iOS security tips
Keeping your iCloud account safe isn’t rocket science. Simple steps like changing passwords, using unique passwords & patterns, not sharing sensitive data could go a long way.
Plus, try and keep the confidential images off the iCloud. If you need, employ photo vault services to guard your photos and videos.
Use these My Photo Stream security tips to protect iPhone photos!
While Apple ensures that its devices and services keep your data as private as possible, the notorious and malicious world can sometimes find the chink in the armor and attack.
So, going some extra steps to maintain your privacy and safety is not a stretch; in fact, it is an absolute necessity! Here are some more iOS privacy tips and tricks you might want to surf through.









Leave a Reply