Someone may be skeptical about installing a keylogger on their device voluntarily. We wouldn’t typically want to see this fellow among applications running on our device, as such kind of programming is traditionally associated with spying malware that tries to compromise our privacy and get hold of our passwords and bank account credentials.
However, recently keylogging was put to good use and is being utilized in the wide array of monitoring tools. There are stand-alone keylogger programs, as well as versatile control applications with featured keylogger options.
What is a keylogger? This is any piece of software or hardware that keeps a log of keystrokes. Not so long ago, keyloggers were only compatible with traditional keyboards. However, touchscreen keyloggers have become possible as well.
They use it to:
- Keep a track of one’s own device, while it’s out of reach;
- Monitor underage children;
- Monitor company-owned devices issued to employees
Concerned parents sometimes use keyloggers to monitor their children’s online activities and whereabouts. Although software designed to block and restrict access to certain content and sites exists, it can be (and very often is) bypassed by tech-savvy children, therefore a keylogger seems to be the only mean of keeping a finger on a pulse of an underage’s cyber life.
Sometimes people would install keylogger programs to secure their phone should they lose it, or see how others use the device given to them temporarily.
Employers sometimes use keyloggers on company-owned iPhones and iPads to assess the employee’s performance and ensure that the device is used only for work-related tasks. In this case, an employee must be aware that the keystroke logging is being performed.
Even if you do not consider installing a keylogger on your device, you should be aware of the possibility.
Moreover, some of them can be hidden, so you may have one on your own device already without even knowing. It’s always better to know what you may face.
Best keyloggers for iPhone and iPad
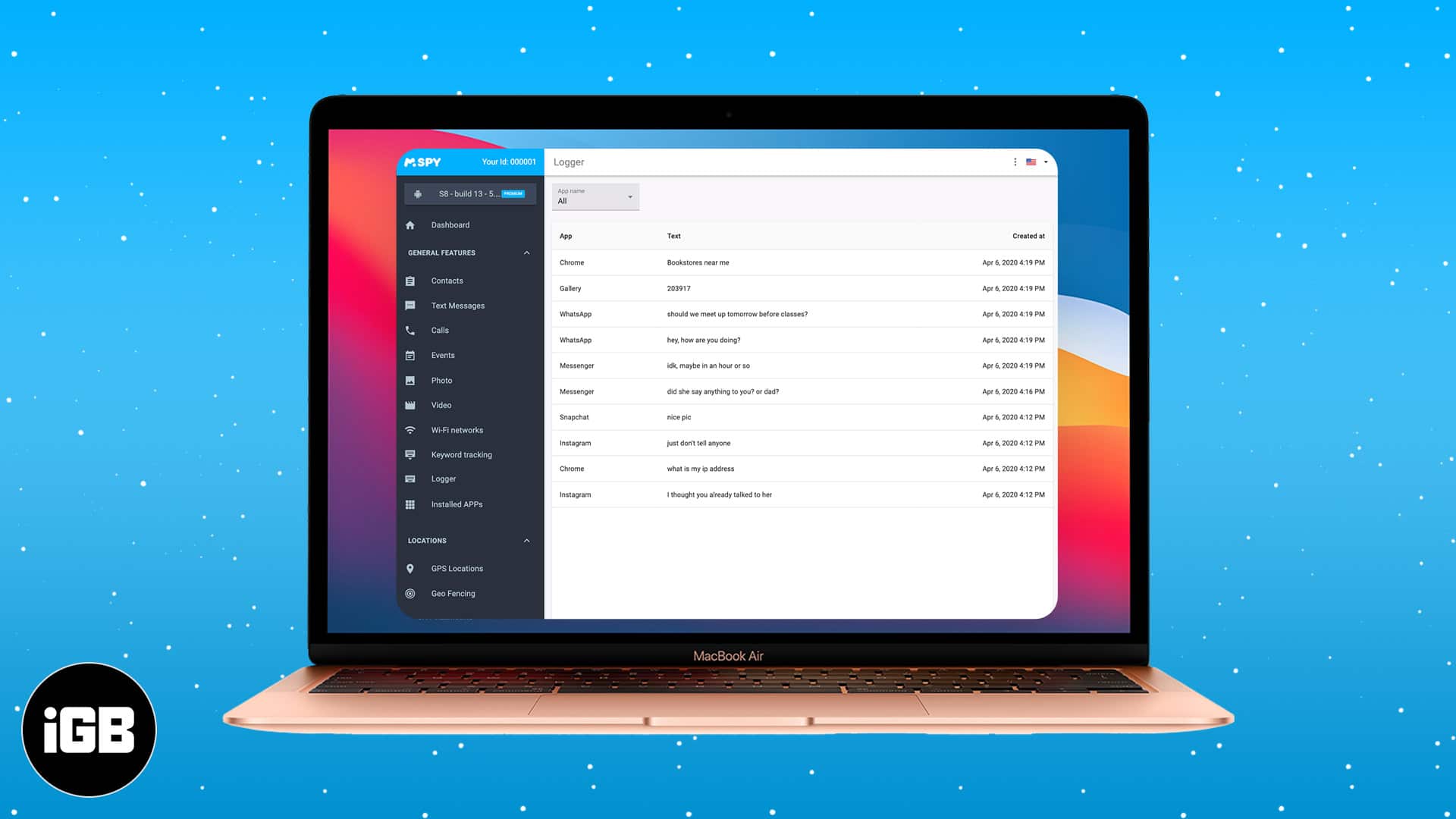
1. mSpy Keylogger
Our top iPhone keylogger is super easy to use and has been specially designed for parents to monitor their child’s activities to ensure safety.
Once installed, mSpy Keylogger remains invisible and runs discreetly in the background to record all activity. It not only tracks browsing activity and chats but also keeps a note of each keystroke to effortlessly stay in the know. That means you can read all sent and received text messages, including those deleted from the target device.
Further, you can know about incoming and outgoing calls and block calls from specified numbers. You can even monitor your child’s location without them knowing.
Of course, you can keep track of your child’s emails and instant messages on various popular apps, including WhatsApp, Facebook Messenger, Instagram, Skype, etc. This is great for invisible supervision to ensure your child is safe from predators and inappropriate content.
In fact, it gives you an enormous amount of control, such as viewing pictures and videos saved on the target iPhone, accessing the contacts and events saved on the phone, limiting the target phone’s access to particular apps and programs, and remotely deleting data and locking the target phone.
With such a wide range of features, it’s a must-have keylogger that every concerned parent can benefit from.
Price: Starts at $29.99 per month
2. iKeyMonitor
iKeyMonitor is one of the best keylogger apps for iPhone and iPad. It not only logs keystrokes but also monitors SMS, WhatsApp, Calls, Facebook, Twitter, and many other things. Once installed on the device, you receive logs through email. There’s no need to login to any dashboard or web service to view the activities.
The primary use of this app is for parents that wish to keep track of their kids’ activity on their iDevices. They can also restrict certain things if needed. The app isn’t available for free, but it comes with trial period before you decide to purchase it.
Price: $49.99/a month
3. Pumpic iPhone Keylogger
This keylogger concentrates on parental monitoring purposes, such as protection against cyber-bullying, online predators, sexting and other inappropriate online behavior from both sides (the child and their interlocutors). The keylogger feature is a part of the Pumpic software, which is visible on the target device, so the person you track is aware of the monitoring (it includes SMS, calls, the web, social networks, pictures and videos, GPS location and many more.)
The information gathered on the target device is sent to the control panel, which is the device you designate.
Main plus: versatility (with options of the remote control panel, geofences, and locking of the device.)
4. FlexiSpy

This one is also offering a keylogger among the array of spying features, which is rather wide: SMS and call logs, e-mail and many social networks messages monitoring, geo-fencing, locking and wiping the phone. However, it’s pretty pricey.
Main plus: “Extreme” version records the surrounding sounds and calls.
5. XNSPY

This is an app that offers more than 35 monitoring features; more for any other app within the same price bracket. While its compatibility is one of its strengths (you don’t need jailbroken iOS devices to use this), you will instantly get used to its smart interface which is simple and user-friendly.
It offers basic as well as advanced features to its users. If you want to only look at the contacts, calls, and SMS information, then its basic features will be enough for you. But if you are looking to get more information that you can rely on its Ambient Recorder and Watchlist features. Watchlist features give instant notifications about certain words, places, locations, and even emails.
With its 24-hour online support and affordable packages, Xnspy is definitely among the top apps in this category.
Main plus: Available on both Android and iPhone. Supports their latest operating systems including Android Oreo 8.0 and iOS 11.
Disclaimer: You should remember, though, that technically, undetectable monitoring software can be classified as surveillance, so make sure you do not use it without other side’s consent (unless the target device belongs to you or your underage children).
About Author: Jana Rooheart is an e-safety specialist and a professional blogger. She lives in Kansas City with her family and works part-time.
You may also like to read:








Leave a Reply